
Business Transformation in the Financial Services Ecosystem
CIO Academy Asia in partnership with Samsung Southeast Asia and Oceania hosted an executive luncheon with digital leaders from
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.

CIO Academy Asia in partnership with Samsung Southeast Asia and Oceania hosted an executive luncheon with digital leaders from

CIO Academy Asia hosted their inaugural session of the #hashtech series at Shiseido’s brand new Regional APAC Headquarters located

Given the red hot startup scene in Israel, can Singapore Inc get a piece of the action? Can Singapore

How do you check that your endpoints such as laptops, tablets and mobile phones are secure while you wander

Wouldn’t it be nice to know exactly what your customer wants when he or she calls your company’s hotline?
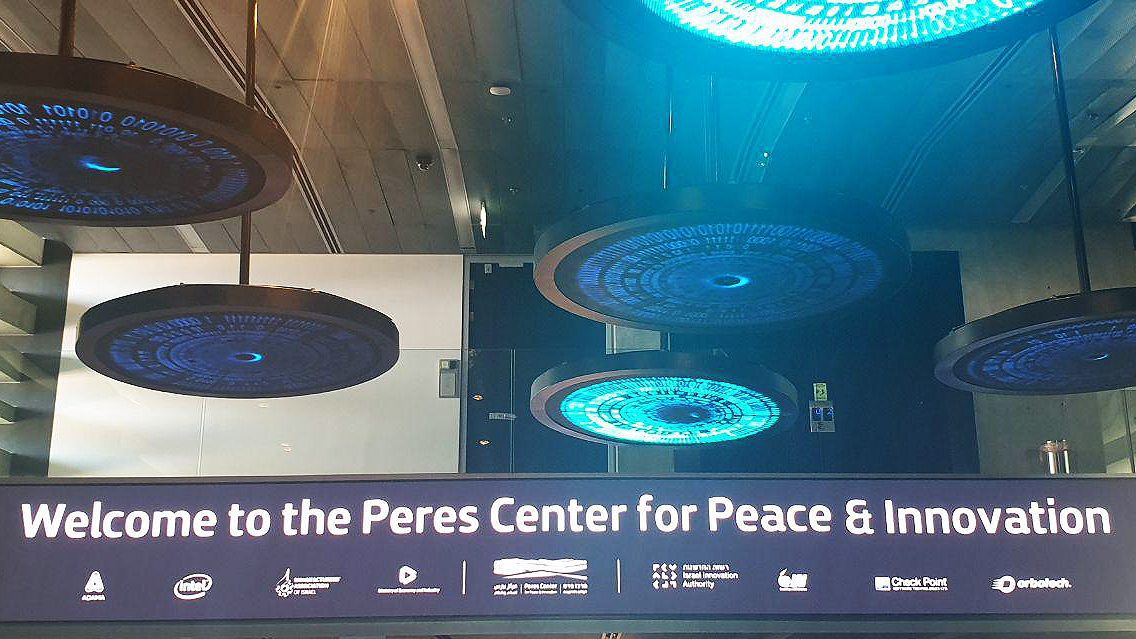
Is there a secret sauce to Israel’s innovation juggernaut? Yes. It can be boiled down to 3Ts & C:

What do you do if hidden hardware devices such as ones attached surreptitiously behind ATM machines, or algorithms embedded

CIO Academy Asia concluded our third edition of the Thought Leadership Forum series, this time with thematic focus on

In partnership with F5 Networks and Kaspersky CIO Academy Asia (CIOAA) held its G-Changers Forum series on the topic:

Given the rapid growth of cloud computing, large enterprises and government agencies, especially those in critical sectors like banking and healthcare, are wary about going all out on the public cloud. The biggest bugbear is security – or lack of it. How do you ensure your workloads on the cloud are secure against malware and hackers?

CIO Academy Asia in partnership with Samsung Southeast Asia and Oceania hosted an executive luncheon with digital leaders from

CIO Academy Asia hosted their inaugural session of the #hashtech series at Shiseido’s brand new Regional APAC Headquarters located

Given the red hot startup scene in Israel, can Singapore Inc get a piece of the action? Can Singapore

How do you check that your endpoints such as laptops, tablets and mobile phones are secure while you wander

Wouldn’t it be nice to know exactly what your customer wants when he or she calls your company’s hotline?
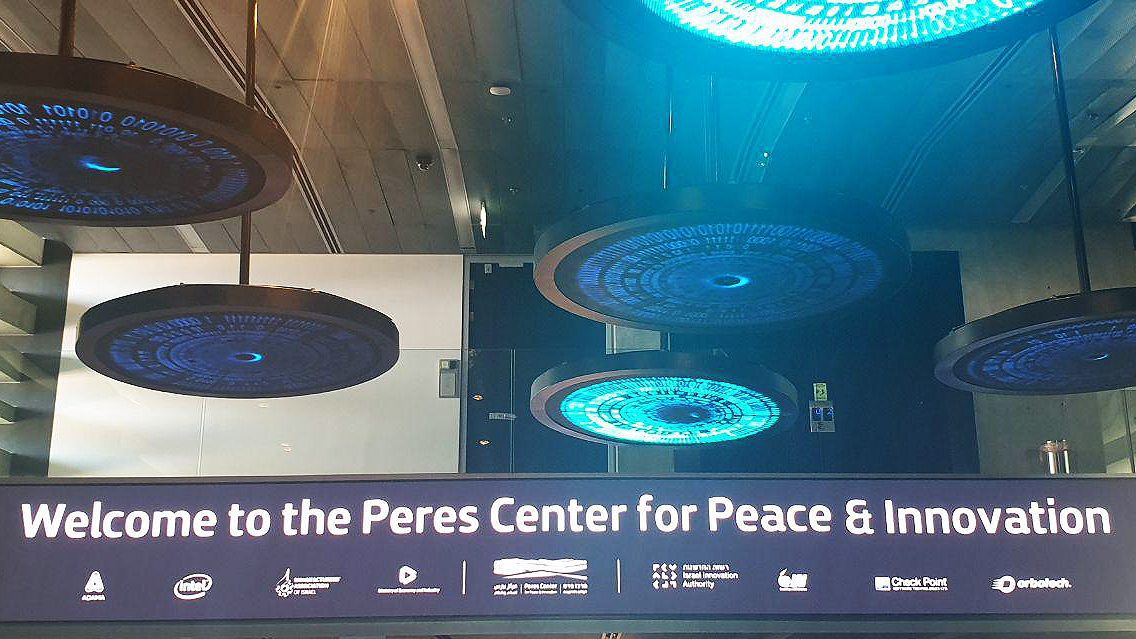
Is there a secret sauce to Israel’s innovation juggernaut? Yes. It can be boiled down to 3Ts & C:

What do you do if hidden hardware devices such as ones attached surreptitiously behind ATM machines, or algorithms embedded

CIO Academy Asia concluded our third edition of the Thought Leadership Forum series, this time with thematic focus on

In partnership with F5 Networks and Kaspersky CIO Academy Asia (CIOAA) held its G-Changers Forum series on the topic:

Given the rapid growth of cloud computing, large enterprises and government agencies, especially those in critical sectors like banking and healthcare, are wary about going all out on the public cloud. The biggest bugbear is security – or lack of it. How do you ensure your workloads on the cloud are secure against malware and hackers?





There was a problem reporting this post.
Please confirm you want to block this member.
You will no longer be able to:
Please note: This action will also remove this member from your connections and send a report to the site admin. Please allow a few minutes for this process to complete.
SPARK brings together a community of technology and business leaders from across Asia.